Uncovering Invisible Privileges: The Ultimate Guide to Mass-Assignment in Registration Flows
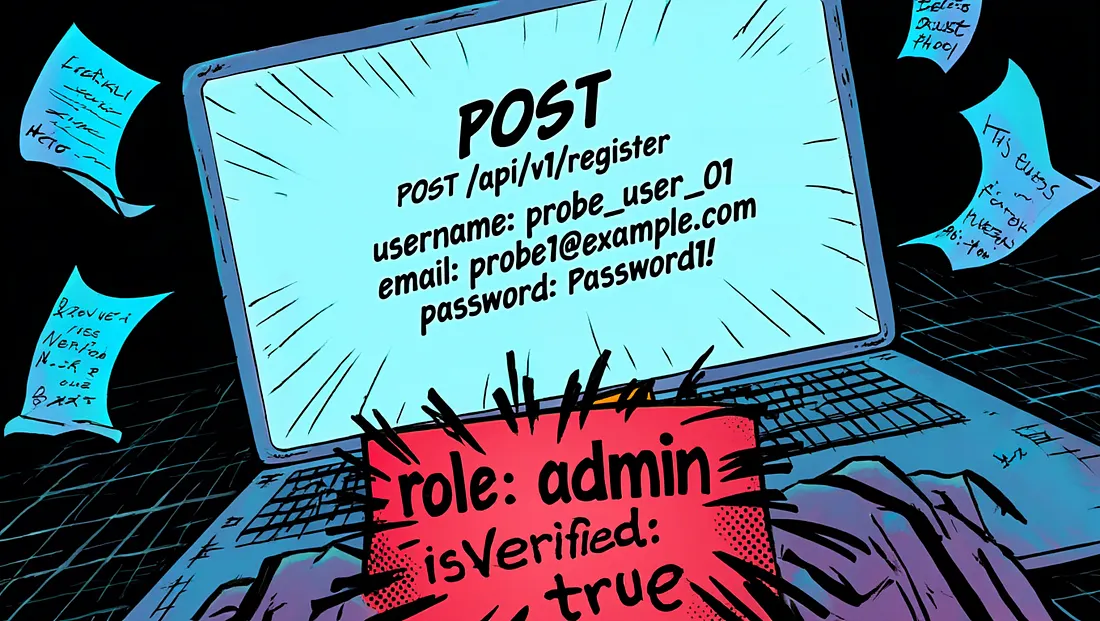
Mass-assignment weaknesses show up frequently in modern APIs, especially in signup endpoints that accept JSON. When the backend automatically maps request fields to internal models without filtering them, attackers can slip in additional parameters and gain privileges they shouldn't have. This guide walks through the most effective JSON payload variations you can use to test registration flows and uncover silent logic flaws.
1.4k reads
461 likes
7 min read